Modernizing processes like identity verification and identity document authentication enable enterprises to streamline operations while eliminating risks more efficiently. Security is paramount in networks as they need to keep the bad guys out to protect the valuable data and assets they keep. It is also crucial for their adherence to regulatory compliance.
Conventional identity proofing methods like Knowledge-Based Authentication (KBA) are often reliant on the concept that only the real identity owner knows the information requested. However, personal data and security questions are easily stolen. Additionally, providing this information only confirms that the person knows them and does not prove that they are who they claim to be.
Similarly, manual ID document checks are often too slow and prone to human error. They can increase security risk, cause inconveniences, and impede productivity. The time used to perform these manual checks could have been used to perform more critical tasks.
Companies must shore up their technologies to confirm their users’ claimed identities in a faster and more secure way. They must adopt modern instruments like a mobile facial biometric identity solution. The identity verification process is completed within a few moments by asking the user to take a quick selfie and undergo an active liveness detection test. Furthermore, using the same mobile device, the person can take a snapshot of their identity document and send it for review. Even if the person’s selfie matches the photo on the identity document, the ID itself might be forged. The automated identity document authentication will compare the provided ID to known templates of specimen documents to ensure that it has the markings of a genuine government-issued credential.
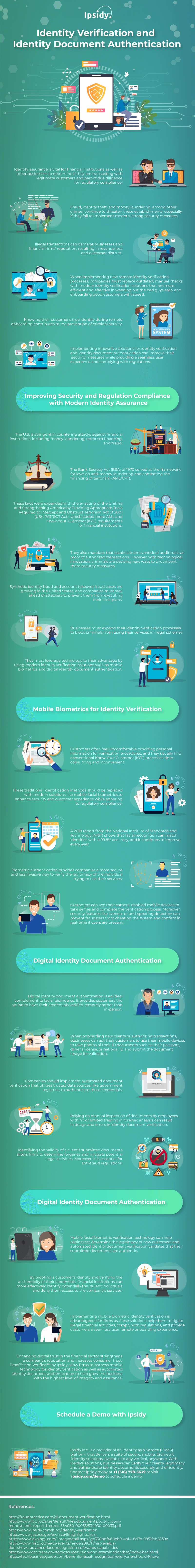
Ensuring that companies only transact with legitimate individuals helps keep their reputation, build consumer trust, and revenue generation. For more information on the importance of identity verification and identity document authentication, an infographic from Ipsidy is provided below.